Amit Praseed

Amit Praseed
Assistant Professor
Office Address:
CSE 202-A, Department of Computer Science and Engineering
Ph. D in Computer Science and Engineering from NITK Surathkal (Thesis Title: Modelling Behavioural Dynamics for Application Layer Distributed Denial of Service Attack Detection)
M.Tech (Computer Science and Engineering - Information Security) from NITK Surathkal
B.Tech (Computer Science and Engineering) from College of Engineering Trivandrum, Kerala University
Educational Qualifications
-
Ph. D in Computer Science and Engineering from NITK Surathkal (Thesis Title: Modelling Behavioural Dynamics for Application Layer Distributed Denial of Service Attack Detection)
-
M.Tech (Computer Science and Engineering - Information Security) from NITK Surathkal
-
B.Tech (Computer Science and Engineering) from College of Engineering Trivandrum, Kerala University
Journals
2024
S. Lakshminarayana, A. Praseed and P. S. Thilagam, "Securing the IoT Application Layer from an MQTT Protocol Perspective: Challenges and Research Prospects," in IEEE Communications Surveys & Tutorials, doi: 10.1109/COMST.2024.3372630
2023
Praseed, A, Rodrigues J, Thilagam SP. 2023. Hindi fake news detection using transformer ensembles. Engineering Applications of Artificial Intelligence. 119:105731.: Pergamon Abstract
2022
Praseed, A, Thilagam SP. 2022. HTTP request pattern based signatures for early application layer DDoS detection: A firewall agnostic approach. Journal of Information Security and Applications. 65:103090.: Elsevier Abstract
2021
Praseed, A, Thilagam SP. 2021. Fuzzy Request Set Modelling for Detecting Multiplexed Asymmetric DDoS Attacks on HTTP/2 servers. Expert Systems with Applications. 186:115697.: Pergamon Abstract
2020
Praseed, A, Thilagam SP. 2020. Modelling behavioural dynamics for asymmetric application layer DDoS detection. IEEE Transactions on Information Forensics and Security. 16:617-626.: IEEE Abstract
2019
Praseed, A, Thilagam SP. 2019. Multiplexed asymmetric attacks: Next-generation DDoS on HTTP/2 servers. IEEE Transactions on Information Forensics and Security. 15:1790-1800.: IEEE Abstract
2018
Deepa, G, Thilagam SP, Khan FA, Praseed A, Pais AR, Palsetia N. 2018. Black-box detection of XQuery injection and parameter tampering vulnerabilities in web applications. International Journal of Information Security. 17:105–120., Number 1: Springer Berlin Heidelberg Abstract
Praseed, A, Thilagam SP. 2018. DDoS attacks at the application layer: Challenges and research perspectives for safeguarding web applications. IEEE Communications Surveys & Tutorials. 21:661–685., Number 1: IEEE Abstract
Deepa, G, Thilagam SP, Praseed A, Pais AR. 2018. DetLogic: A black-box approach for detecting logic vulnerabilities in web applications. Journal of Network and Computer Applications. 109:89-109.: Elsevier Abstract
Conferences
2015
Praseed, A, Sudheesh RK, Chandrasekaran K. 2015. Efficient privacy preserving ranked search over encrypted data. 2015 IEEE Recent Advances in Intelligent Computational Systems (RAICS). :128-133.: IEEE Abstract
Professional Experience
-
Assistant Professor in Computer Science and Engineering at NIT Calicut (12 December 2022 - )
-
Assistant Professor in Computer Science and Engineering at IIIT Sri City (1 December 2020 - 10 December 2022)
-
Adhoc Faculty in Computer Science and Engineering Department at NIT Calicut (2 September 2020 - 18 November 2020)
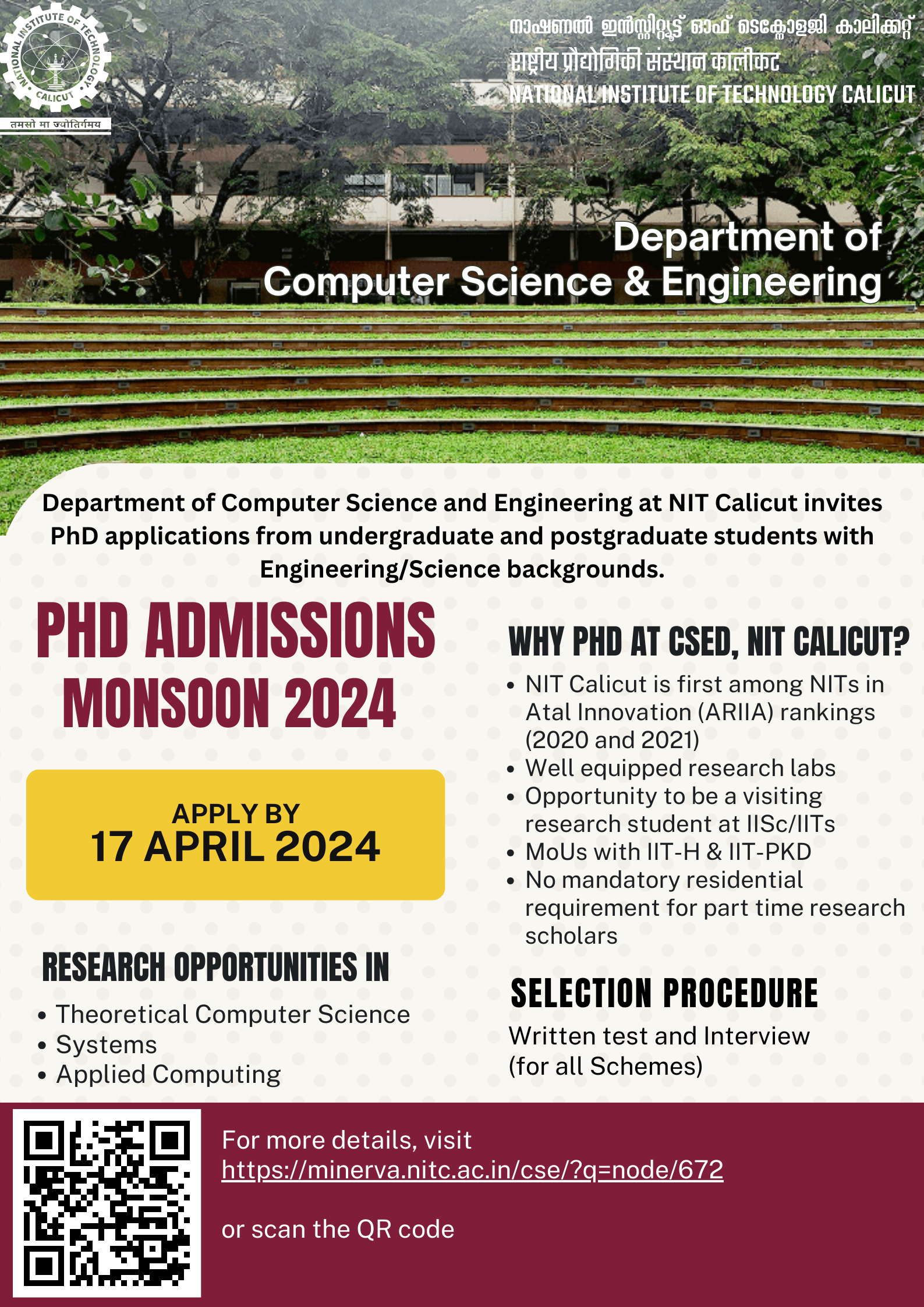
PhD Admissions (Monsoon 2024) at NITC
Applications are invited for the admissions to the PhD programme at CSED, NITC for the Monsoon 2024 Session.
Eligibilty and Other Details can be found HERE.
Selection Procedure at CSED: Written Test followed by Interviews
Last Date to Apply Online: 17 April 2024
Link to Apply: https://dss.nitc.ac.in/mtechapp/phd/frmLogin.aspx
Fake News Detection
Fake news is one of the biggest threats in the modern world. With the advent of social media, it has become effortless to create and dissemiate information. However, verifying the authenticity of this information is a daunting task, requiring extensive applications of techniques from knowledge modeling and artificial intelligence. Recently, stance based fake news detection using transformer based language models have gained attention. However, the performance of these techniques on existing datasets remains comparatively low. The use of ensemble techniques, knowledge modeling, and explainable AI can improve the existing techniques considerably.
Link to my paper on the use of transformer ensembles for detecting Hindi fake news can be found here.
Authorship Attribution
Experienced readers can quickly deduce the author of a prose - nightmarish scenarios are inherently Kafka-esque, while long, complex sentences where delve into a character's consciousness is considered classic Dostoevsky prose. Writing style is often considered to be unique enough to pinpoint the author. Authorship attribution, at its very core aims to do just that - given a particular piece of text and a set of candidate authors, we aim to predict the author of the given piece of text. Although traditionally dominated by syntactic features such as n-grams, the rise of Large Language Models (LLMs) have made this area of research relativley active and interesting. The same line of reasoning can be applied to identification of authors for source codes, which finds considerable applications in the field of digital forensics, plagiarism detection etc.
Parallel to this line of thinking, it is also possible to rephrase this problem into identifying whether a given piece of text (or code) was generated by a machine or not. This line of reseach has important implications for the field of academic integrity, plagiarism detection, fake news detection and so on.
Modelling User Behaviour for Detection of Cyber Attacks
Security of web applications and services is of crucial importance in the modern era when much of our transactions is being done online. However, this is by no means easy - given the multitide of attacks that plague us, such as SQL injection, XSS, CSRF, parameter tampering, session violation etc. In addition, there are protocol vulnerabilities, stemming from either weak protocol specifications or vulnerabilities in the implementations. The difficulty in identifying these attacks is due to the fact that a simple rule-based system cannot be used to define these attacks, and often the description of these attacks will simply be "something that normal users wouldn't do". Thus it is necessary to encapsulate what constitutes as legitimate user behaviour, and using this model to identify deviant access to a system. This can be done using simple automata based modelling, scoring mechanisms, or through sophisticated ML/DL models.
My previous works related to modelling injection and logic vulnerabilities can be found below:
DetLogic: A black-box approach for detecting logic vulnerabilities in web applications
Black-box detection of XQuery injection and parameter tampering vulnerabilities in web applications
My papers on DDoS attack detection through behavioural modelling can be found here:
Modelling behavioural dynamics for asymmetric application layer DDoS detection
Multiplexed asymmetric attacks: Next-generation DDoS on HTTP/2 servers
Fuzzy request set modelling for detecting multiplexed asymmetric ddos attacks on http/2 servers
Full Time
- Shilpa Sarat (ongoing)
- Nasmath C (ongoing)
Talks Delivered
| Sl. No. | Talk Title | Event/Programme | Institute | Date |
| 1 |
Distributed Denial of Service Attacks in the age of AI/ML |
5 Day Workshop on Machine Learning and Deep Learning Techniques for Cyber Security |
N.M.A.M. Institute of Technology, Udupi | 12 January 2024 |
| 2 | Introduction to Machine Learning | Visiting Faculty Programme, Govt. of Kerala | Government College of Engineering, Kannur | 25 March 2024 |

